19 March 2017
Ransomware for Industrial Control Systems (ICS) is a scaring idea. The research paper ‘Out of Control: Ransomware for Industrial Control System‘ by David Formby, Srikar Durbha and Raheem Beyah from the Georgia Institute of Technology is really worth reading.
The researchers study several attack vectors and run a proof of concept (POC). In addition, they give some hints for mitigation of this new risk in the ICS / SCADA domain.
In the simplest case, if the PLC is connected to the internet, the cyber-criminal can attack the PLC directly. A more dangerous, but also very promising way is to start an attack on a workstation located in the corporate network and use this system as base camp for the access to the production network.
In the past weeks I prepared a speech for a workshop about “Safety and security in plant safety”. In the IIoT, the digital world acts upon the physical world. With this, flaws in the IIoT software may create a safety problem. For example, if a PLC or other SCADA components are attached to the internet, cyber criminals can exploit such flaws and compromise the integrity of the systems or implement ransomware on the systems. In the worst case, if e.g. the SCADA system controls a critical infrastructure like a power grid, this may result in a blackout. And operators of critical infrastructures will pay definitely any ransom to avoid a blackout.
The attack vectors described above are the native way for accessing industrial facilities and critical infrastructures. Besides the PLC, lots of other components like switches or HMI panels are connected more or less intentionally to the internet today. My colleague Christoph Thust from Evonik calls this the Digital Carelessness.
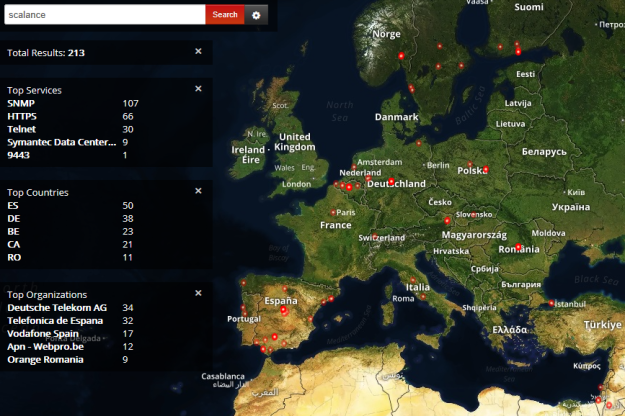
A plain SHODAN search for ‘SCALANCE‘ results in 213 hits. These network switches are more or less exposed to the internet. If a cyber attacker can hijack such a switch, he gains full control of the production network.
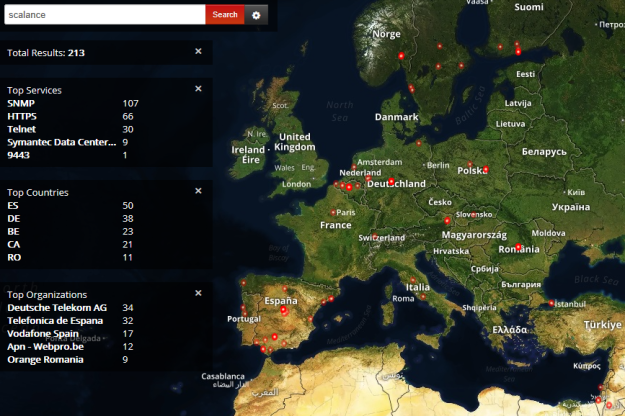
Shodan Scalance Search. Click to enlarge.
A search for ‘SIMATIC HMI‘ results in 103 hits. This HMI panels are directly attached to the internet, lots of them can be viewed with WinVNC, some of them can be fully operated by EVERYONE.

Shodan Search HMI. Click to enlarge.
And, above all, HMI panels attached to the internet can be used as base camp for an attacker’s lateral movement in the production network.
Although ransomware is a really big issue today, the effort to rollout ransomware in a SCADA environment is high compared to the effort of plain attacks to unsecured SCADA system components.
The good news is, that the vendors of SCADA components already offer the elementary technology and strategies for their secure operation. But improvement of the basic security technologies is of crucial need for efficient use in the production domain.
The bad news is, that neither the engineering service providers nor the plant operators are fully aware of cyber-threats and their impact on plant operations and safety. The above examples make clear that the mitigation measures and defense strategies provided by the technology vendors are not followed.
From my point of view we need to start early in the construction process with considerations of cyber security. Security gates must be added to each construction phase. And during handover to the operator, a final pen test must be performed. As soon as Security by Design becomes an integral part of the Industrial Plant Life Cycle, the era of digital carelessness will end.
Have a good weekend.